CVE-2024-38163 and CVE-2024-38202 are both EoP vulnerabilities in Windows Update Stack and were assigned CVSSv3 scores of 7.8 and 7.3 respectively. CVE-2024-38163, if successfully exploited could result in gaining SYSTEM privileges. Microsoft has noted that users don’t need to take any action for this vulnerability as it is only exploitable at run time and the impacted version of WinRE has been superseded by a new version.
CVE-2024-38202 was disclosed and presented at BlackHat USA 2024 and DEF CON 32 by SafeBreach Labs researcher Alon Leviev prior to the August 2024 Patch Tuesday release. The vulnerability which exists in Windows Backup, allows a user with basic privileges to “reintroduce previously mitigated vulnerabilities or circumvent some features of Virtualization Based Security (VBS)”. Leviev identified the vulnerability in the Windows Update mechanism that could allow unauthorized elevation of privileges by enforcing the downgrade of system components. This vulnerability exposes systems to previously patched exploits, making them susceptible to attacks that could leverage these old vulnerabilities. Microsoft has noted that “an attacker attempting to exploit this vulnerability requires additional interaction by a privileged user to be successful.” Microsoft issued an advisory in coordination with this disclosure at Black Hat.
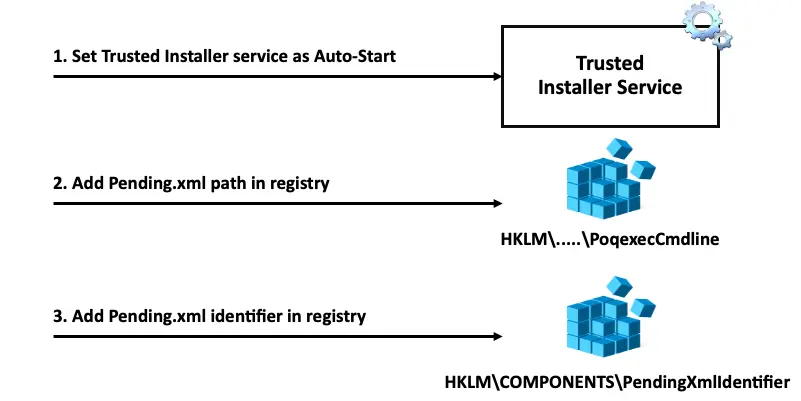
Source: Leviev's SafeBreach Blog
